Released today:
It can be said that anything that measures the whereabouts of a person in a public place (even if by proxy of a device) , then the law applies.
Its the same sort of thing as follows
Security Camera
You can do this if the camera is on your property (and put warning signs up) - It can be said that you control this space and because people have been warned, they have to give their implicit consent if they want to enter your property (i.e it is not a public space where the reverse applies - someone can refuse to be filmed).
GPS tracker
If you put a GPS tracker in a car to track the person without them knowing, a jail term awaits
you
Readme.md updated 
“Disclosure: The Paxcounter code stores scanned MAC adresses in the device’s RAM, and keeps it in RAM temporary for a configurable scan cycle time (default 240 seconds). After each scan cycle the collected MAC data is erased from RAM. MAC data never is transferred to the LoRaWAN network. No kind of tracking and no persistent storing of MAC data or timestamps on the device and no other kind of analytics than counting is implemented in this code. Wireless networks are not touched by this code, but MAC adresses from wireless devices as well within as not within wireless networks, regardless if encrypted or unencrypted, are made visible and scanned by this code. The same applies to Bluetooth MACs, if the bluetooth option in the code is enabled.”
Unfortunately, I think the use of device brings itself under the law.
How much the law would look at it is the unknown question though.
IMO, It don’t think the time you store the data makes a difference. Technically the gif you show is proving that you are breaking the law (even though you are doing so being ignorant of it).
Also, the use of long range comms potentially means another problem - you are involving TTN.
I think you should be saying that the user of software has to use it at their own risk, and the scanning area should only be done within a privately owned property which has appropraite signs.
You should also say that the device must not be used in public and any data used only for private research etc etc etc.
All of this is my thinking, you might be better getting proper advice?
.
i added another note to readme:
“Note: If you use this software you do this at your own risk. That means that you alone - not the authors of this software - are responsible for the legal compliance of your application of this software and/or usage of a device created with this software. You should take special care if you plan metering passengers in public areas and/or publish data drawn from doing so.”
But i am not responsible for what user do with this open sourced software.
I added explicit hints in the documentation.
Whether an application based on this software is illegal, depends on the individual use case and law of the country where it happenes. GDPR does not say that passenger flow metering is generally illegal, it depends on how it is carried out.
I’m not familiar with the term “paxcounter”, and a quick google search didn’t give me conclusive information. Maybe add a section to the readme describing what a paxcounter is/does?
GDPR states any processing of user identifying data requires the processor to be able to produce explicit permission to process it for this purpose granted by the user. That means a user has to provide you with permission (not by not removing some check mark but by explicitly setting it).
It also states you need to inform the user what the information will be used for and it is commonly suggested you remove all identifying data as soon as you’re done processing it.
in the Netherlands they call it ‘sleepnet’ … next week we can vote if we allow our government tapping all our daily/business (digital/radio/phone ect) communications … and store it for a very long time for later analyses.
Nobody wants it but it will be implemented for sure… 
I am almost certain that TTN needs to provide means to 'tap when secret services demands that.
In the Leipzig fair halls i saw this sticker on a toilet door, not sure what kind of counting technology was installed there.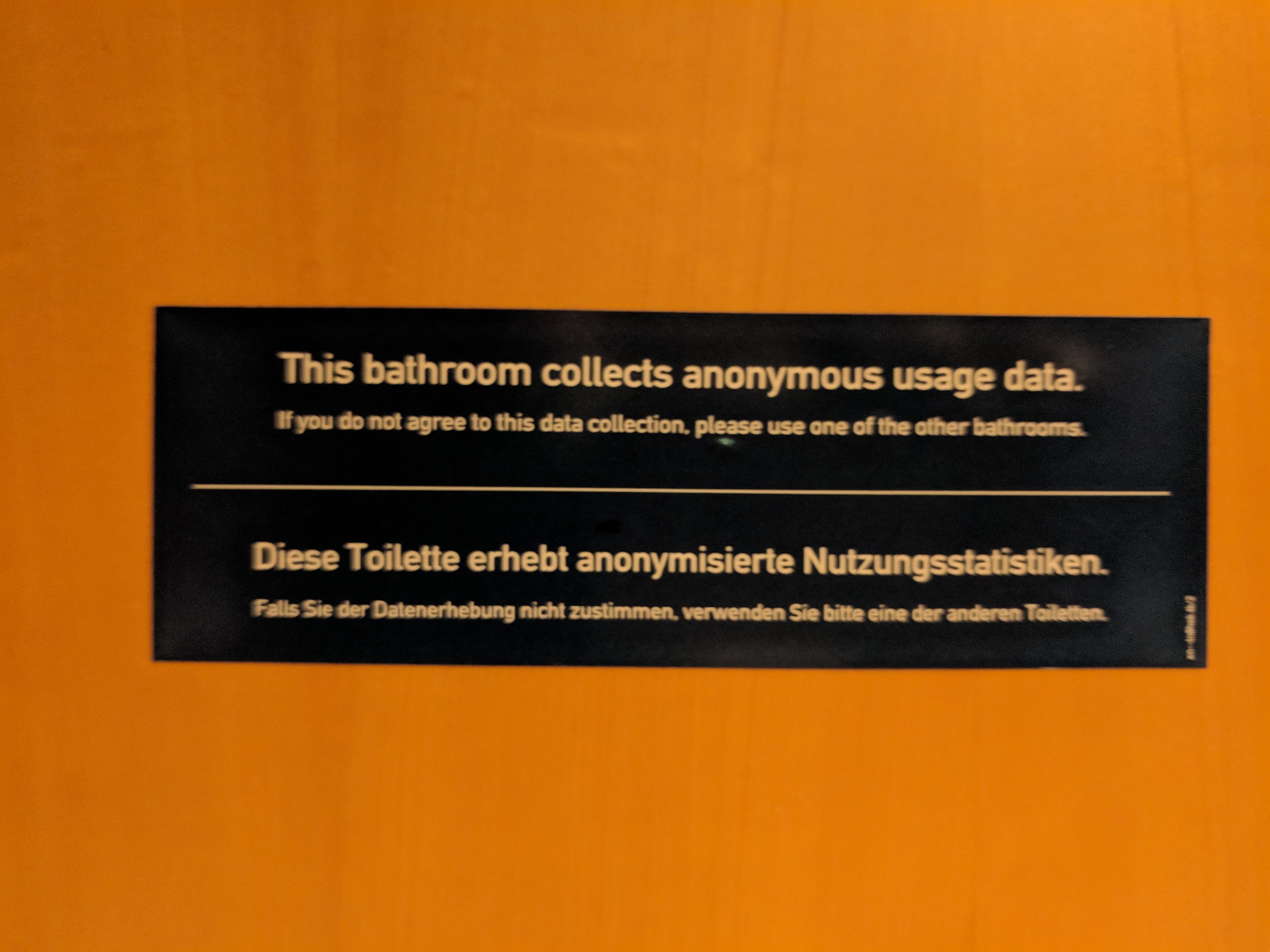
yes - Its a fascinating area.
As you are probably aware, the sneaky way to gain consent is by offering free wifi.
For quite some time now, it’s been used to track customers. i.e. measure footfall within a store - where one goes, date/time, how long you stay there and the holy grail - a link to your spending profile / history with loyalty card references,
How tracking customers in-store will soon be the norm | Big data | The Guardian.
The tech is already well established, its the clever “joining the dots and data mining” bit thats not quite there yet.
I guess one of the reasons why they are able to comply with regulations is because measurement is within their property/store. Where it is getting out of hand is the joining of separate loyalty card data, so people are effectively tracked wherever (all by consent of course).
I went to a talk recently where a large database provider mentioned they are trailing such a system for a major food retailer in the UK - the real people the law is aimed at.
The purpose of my project is NOT tracking, just counting, and doing that while respecting privacy concerns with best effort.
Okay, what is still missing in code is hashing&salting the MACs before storing them in RAM. That would be a privacy improvement. Maybe some one can code this and open a pull request?
Since there is no other analytics in the code besides storing and counting unique MACs over a short time, i think this solution is much more respecting privacy than cloud appliances, which probably push much more data to some servers wherever and store it forever.
If you do not explicitly ask for consent for this purpose it will be illegal.
Yes true, There is usually a box you have to tick “data given to our partners” or something.
This is from 2013 (just shows how long its been going on)
20 mins in for wifi analytics
29 mins in for opt in
From what I understand that is no longer sufficient. You need to explicitly mention the data will be used to track your position for behavioral analysis. Not that it will reduce the number of people allowing them to use the data, free Wi-Fi is far more valuable then your privacy… ![]()
It seems that is more a fun project or show case than a real world application. Because all iphone devices sending random mac adresses for preventing sniffing and tracking the person. Many Android devices has the same feature, so you will count one person with an iphone as many persons. Same is when on one device BLE and Wifi is active, it has different mac addresses, so you will count one person as two.
But this project is very good to share ideas and inspiring other people to create appplications with Lora. In our TTN Freiburg community, we already discuss about that project and will be discussing that with our local public transportation provider (they have interest in lora, but no usecase at the moment). We have the idea, not to count Wifi or BLE, we uses radar to detect entering or leaving people in a tram.
The randomization will probably disrupt this use case in next years, since Google, Apple and Microsoft (Win 10 already has randomization) are not interested in loosing their advantages on data crawling.
But currently the code seems to generate surprisingly good results.
There are some articles on the web which describe how wifi tracking can be possible even with randomization, if “fingerprinting” algorithms are used, that sniff and store additional data, e.g. timing behaviour of wifi clients. But i’m not planning to enhance my code with those privacy sensible features. The code shall, as you explain, give a simple but impressive use case example for what can be done (and, at the same time, should not be done) with sensors in an LP WAN.
Yes, as I understand it, current radar techniques (or PIR) don’t differentiate between people i.e. the sensing process does not identify and store some sort of “Tag” per person, and this is why it would be exempt from the law.
N.B. When you have “free wifi”, it doesn’t matter if your phone has a random mac address, it is identified and the mac address is fixed whilst you are (automatically) wifi connected.
Its interesting that “Free wifi” is used as a vehicle to get consent (which will be more obvious soon as Kersing says), and also to get round Mac address randomization.
There are some studies on the net on this topic and what’s coming beyond wifi randomization: device fingerprinting.
Trials for automatic counting in public transport vehicles like trains and buses have a long history. Different technology approaches were carried out with different sensors. But in all cases known to me, the results were unsatisfying, especially when it comes to count absolute numbers of passengers which is often needed for yield split contracts.
But if relative numbers are sufficient, e.g. for shifting people to uncrowded parts/doors of trains, crowd level based metering can do the job.
As long as wifi counting achieves acceptable differential results (and this could be possible even if randomization becomes standard), this brings a good fit to this use case. Because it is much easier to deploy a wifi based paxcounter on trains/buses, compared to the retrofit installation of radar or optical sensors.
Another option to count people in trains/buses would be to use videoanalytics behind the vehicle’s on board CCTV system, if it has one.
In all these cases it makes sense to have the illelligence of counting in the sensor (“edge computing”), not on the server side. This keeps privacy issues off the network and gives the chance to use LP WANs like TTN for transmission of the metered results, instead raw data.
That’s why i began the paxcounter project. It shall give a practical PoC for this purpose. You don’t need e.g. a cisco meraki with lots of privacy intrusion before data is anonymized, only to count people. The sensor itself should anonymize data as neartime as possible.
During any PoC, do you think this system can listen to phone signals without the need to warn people that it is being done?