The device should use OTAA (a hardcoded ABP DevAddr is not supported).
For OTAA, each LoRaWAN 1.0.x device needs an Application Identifier (AppEUI), Device Identifier (DevEUI) and secret Application Key (AppKey; not the secret application session key, AppSKey). With TTN, all these can be set to any value using TTN Console:
-
In the application settings:
- add the AppEUI
Each application can have multiple values for AppEUI.
-
In the device settings:
- select the AppEUI as added to the application in step 1
- manually enter the DevEUI
- manually enter the AppKey
To use a LoRaWAN 1.1.x device on a 1.0.x network:
- Use the 1.1.x JoinEUI as the 1.0.x AppEUI
- Use the 1.1.x DevEUI as usual
- Use the 1.1.x NwkKey as the 1.0.x AppKey
- Ignore the 1.1.x AppKey
(LoRaWAN 1.1 uses the new NwkKey for the OTAA join. If the OTAA Join Accept indicates it’s connected to a LoRaWAN 1.0.x server, then the device will fall back to 1.0.x.)
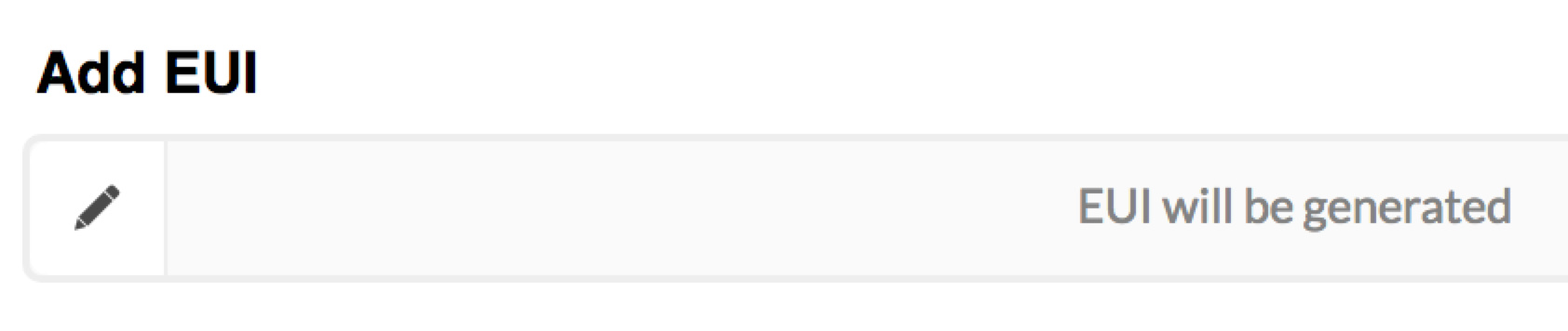
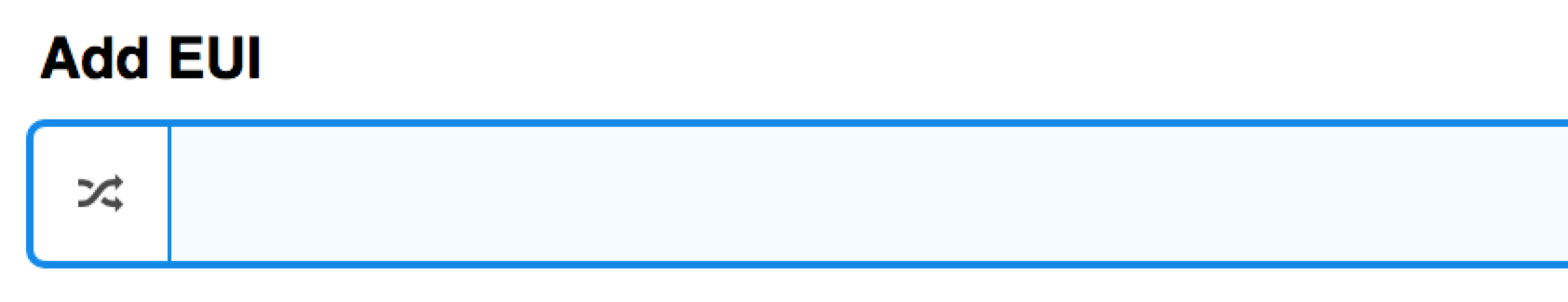
To enter a value rather than having one generated, click the pencil icon to allow for manual input: